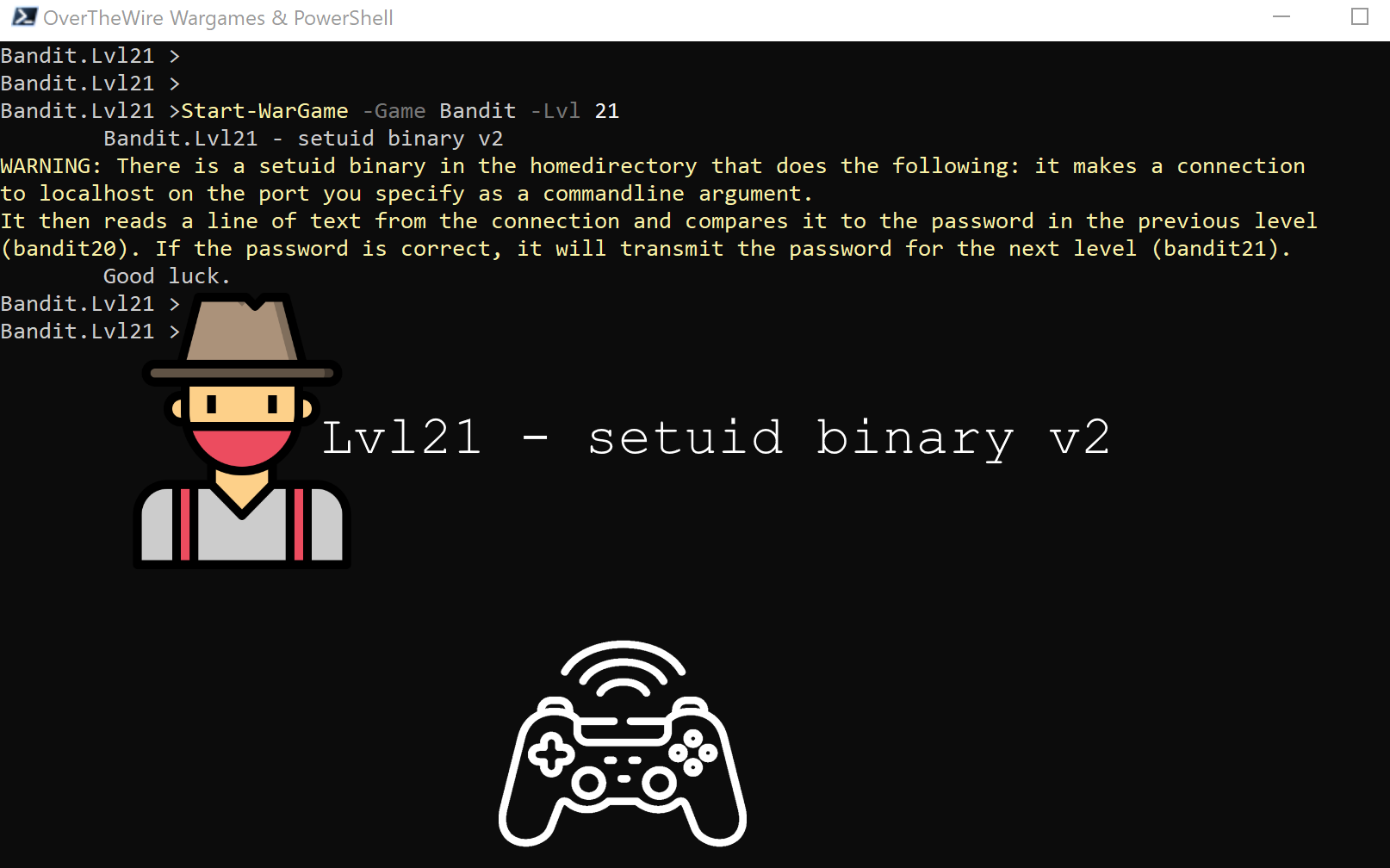
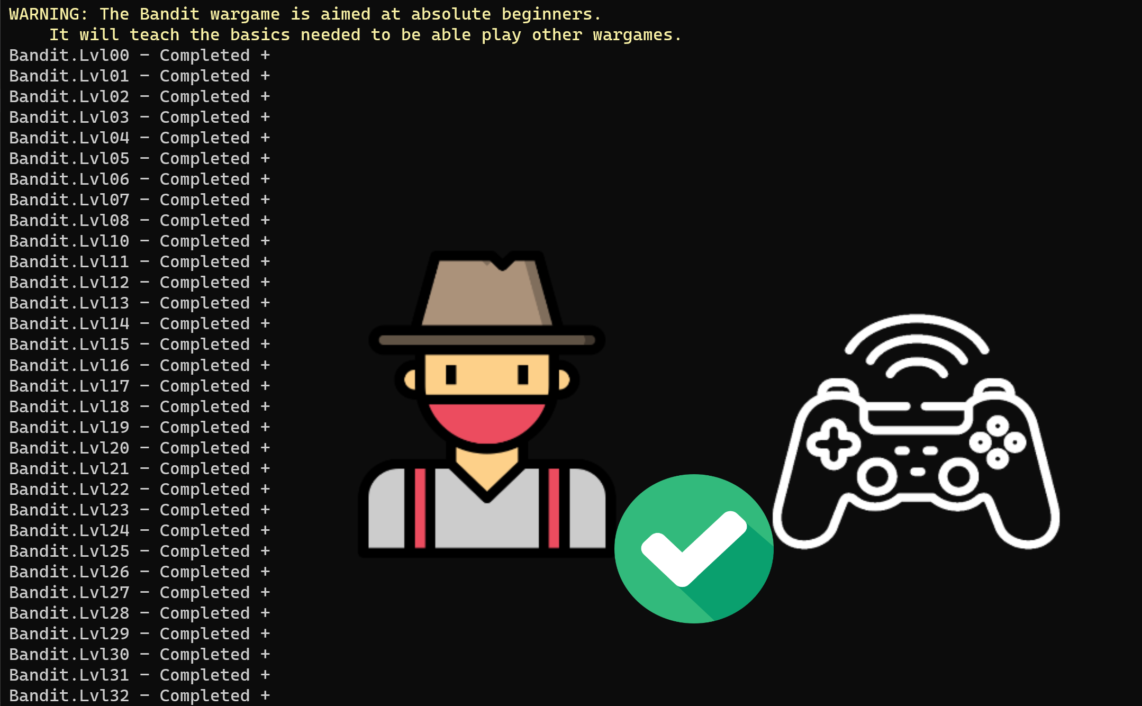
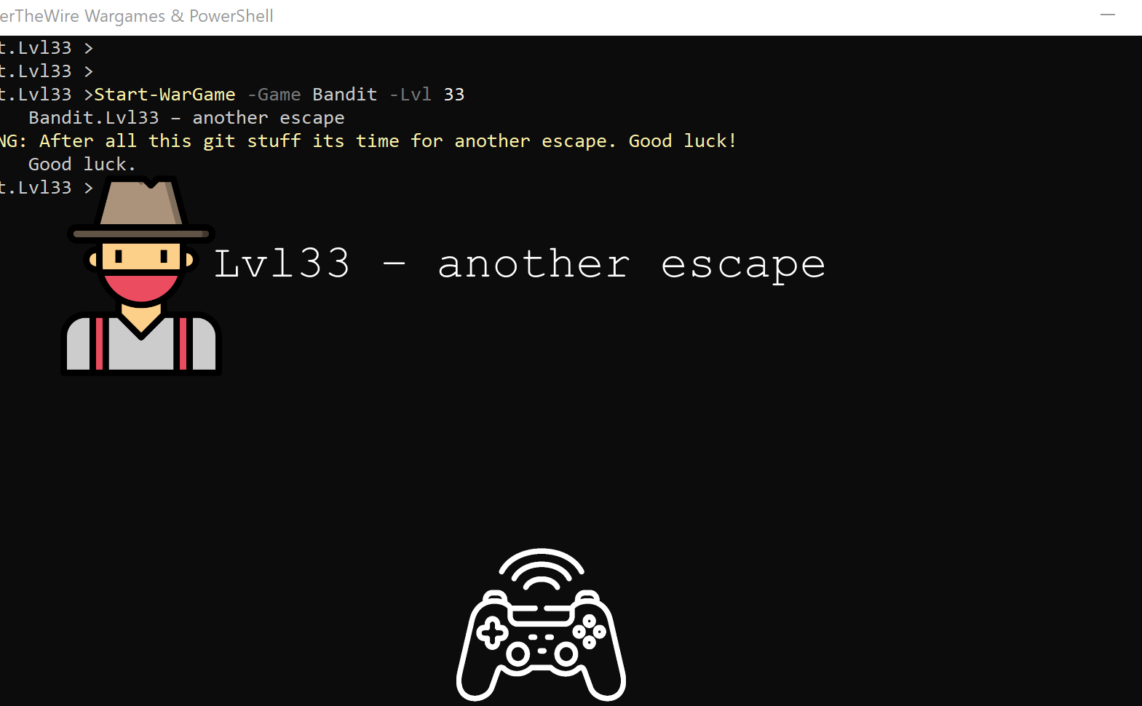
This is the blog post series related to Bandit Wargame from OverTheWire community. It is my attempt to challenge myself and play some Wargames as suggested by CTF Field Guide.
Previous challenge – Lvl20 – setuid binary v2
Goal
“There is a setuid binary in the homedirectory that does the following: it makes a connection to localhost on the port you specify as a commandline argument. It then reads a line of text from the connection and compares it to the password in the previous level (bandit20). If the password is correct, it will transmit the password for the next level (bandit21).“
Reference: https://overthewire.org/wargames/bandit/bandit21.html
PowerShell Modules Used
Key Linux command(s)
ncsetuid
Next level – Lvl22 – cron & crontab
Thanks a lot for reading.

Icons made by surang & Freepik from www.flaticon.com.